Introduction
The Challenge of Multi-Account Compliance in AWS
Organizations leveraging AWS rapidly scale resources and grow into multi-account environments to support a multi-boundary security architecture. However, this leads to fragmented configuration visibility across these accounts, which necessitates the need for the AWS Config Aggregator. This is because it results in inconsistent compliance monitoring across teams, diluting the benefits of multi-boundary for secure architecture best practices. Also, there is difficulty maintaining centralized governance oversight, which is core to architectural security. Additionally, it limits cross-account configuration oversight, essential for boundary controls. This fragmented visibility is often complemented by centralized monitoring layers such as CloudWatch metrics and dimensions, which provide consistent operational insight across accounts.
AWS Config Aggregators Provide Centralized Visibility
The solution is therefore to aggregate configuration data across multiple AWS accounts, which is the job of the AWS Config Aggregator. It provides a centralized view of compliance status across regions, ensuring consistent monitoring across teams. Additionally, it supports centralized governance oversight by enabling organization-wide configuration monitoring through AWS Organizations. Furthermore, it simplifies auditing and governance oversight, eliminating the need to perform these activities separately for each account. Overall, there is a unified compliance reporting form distributed across environments, enabling centralized governance and cross-account oversight.
What Is an AWS Config Aggregator
AWS Config Aggregator Overview
AWS Config Aggregator is a key feature of AWS Config that provides centralized visibility of AWS resource configuration across accounts and regions. It performs aggregation of configuration and compliance data collected by AWS Config instances in each account and region. Hence, it enables cross-account monitoring across AWS environments rather than monitoring each account separately. Additionally, this allows visibility into multi-region configuration from a single view rather than a view for each region. This establishes the foundation for centralized compliance management.
How AWS Config Aggregators Work
Each AWS Config instance has recorders that capture the configuration state of resources within its particular account and region. The other key role is that it applies AWS Config rules to evaluate compliance of each resource within its account and region, as covered in Keeping AWS Environments Compliant with AWS Config Rules. Invariably, there is a central account with an AWS Config Aggregator that collects configuration and compliance data from all Config instances. This collected data is then aggregated across multiple AWS accounts and regions. The key benefits are cross-region configuration visibility through centralized queries and the display of aggregated results in a central monitoring account.
Role in Enterprise Cloud Governance
AWS Config Aggregators are essential for enterprise cloud governance since they provide organization-wide compliance visibility across AWS accounts in centralized views. They also enable the detection of configuration drift in distributed environments, allowing consistent compliance maintenance across accounts and regions. This provides centralized oversight for security and compliance teams in monitoring resource compliance across all accounts and regions. Additionally, it supports governance frameworks and audit processes that need to evaluate resource compliance across all accounts and regions. This makes them the foundation for automated compliance monitoring and remediation.
Why Multi-Account Compliance Requires Aggregation
Multi-Account Architecture in Modern AWS Environments
Security Doesn’t Start with IAM — It Starts with Architecture states that organizations that scale resources should set up multi-account environments. AWS Organizations enables companies to establish structured multi-account environments often resembling their corporate structure. Therefore, companies use these accounts as security and operational boundaries. Furthermore, this allows the separation of production, development, and shared services accounts. Consequently, there are independent AWS Config recorders, one at each account and region. This results in configuration and compliance data being distributed across all these accounts and regions.
Fragmented Compliance Visibility Across Accounts
Since there are independent AWS Config recorders distributed across accounts and regions, configuration data is generated in each AWS Account independently. Furthermore, AWS Config rules produce separate compliance evaluations in each account and region. Consequently, cross-account visibility of configuration and compliance is severely limited for security teams. They have to manually perform any configuration reviews and remediation across multiple accounts and regions. This is highly inefficient and increases complexity when compliance monitoring is performed manually. This significantly increases the risk of any configuration drift going undetected due to fatigue and repetitive tasks.
Aggregation Enables Centralized Governance
Aggregation consolidates configuration and compliance data across accounts and regions, eliminating manual configuration reviews and remediation. Subsequently, it provides organization-wide visibility into configuration and compliance across AWS accounts and regions in a single view. This enables security teams to perform centralized querying of configuration state and compliance across environments. Subsequently, they can generate cross-account compliance in a single report, simplifying the process and governance reviews. This enables scalable monitoring of configuration compliance across large multi-account architectures.
How AWS Config Aggregators Work Across AWS Organizations
AWS Organizations as the Foundation for Multi-Account Governance
Following security best practices, organizations that scale up resource usage will group them into trust boundaries corresponding to AWS accounts. It follows that they require centralized management of these AWS accounts; otherwise, resource management and security are unwieldy. The Organization Unit (OU) is an AWS construct that allows companies to group accounts by environment or function. These accounts correspond to trust boundaries following the security architecture approach in Security Doesn’t Start with IAM — It Starts with Architecture. These Organization Units form a hierarchy and establish a central security or governance account within the organization. This allows independent AWS Config recorders to operate on a per-account and per-region basis, with configuration and compliance data distributed across member accounts.
Aggregating Configuration Data Across Member Accounts
Given that configuration and compliance data are distributed across member accounts, the AWS Config Aggregator is deployed in the central governance account. The AWS Config Aggregator is subsequently granted authorized access to AWS Config data from the member accounts. It therefore collects configuration state and compliance results from AWS Config in each member account and each region. It subsequently aggregates AWS Config rule evaluations across these accounts for centralized display and analysis. This provides centralized visibility into cross-account and cross-region configurations without accessing individual accounts or regions. This also enables centralized querying of resource configuration across the organization without manually collecting data from the different accounts or regions.
Centralized Compliance Monitoring for Security Teams
AWS Config Aggregators provide organization-wide visibility of configuration compliance of resources for all accounts and regions. Additionally, it provides centralized monitoring of AWS Config rule evaluations applied to the resources for potential remediation. This also includes the ability to drill into a single-account view of compliance posture across the environments, besides aggregated views. This enables security teams to more quickly identify configuration drift across accounts without resorting to more manual means. Having configuration and compliance data in one location significantly simplifies audit preparation and compliance reporting on that data. This allows governance monitoring to scale as AWS environments grow.
Architecture Pattern for Centralized Compliance Monitoring
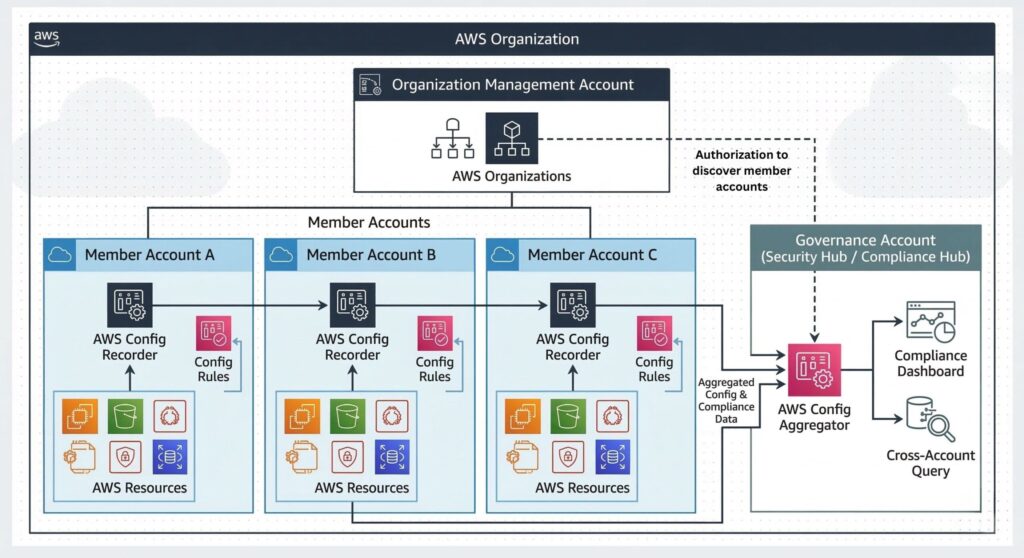
Central Governance Account as the Compliance Hub
Security best practices stipulate deploying the AWS Config Aggregator in a central governance account within AWS Organizations. The aggregator has permission to access AWS Config data across all accounts and regions, thus establishing visibility into organization-wide compliance. This provides security teams with a centralized monitoring point for configuration and rule evaluations and more rapid configuration drift detection. Audit teams have all compliance data located in one place for analysis and reporting.
Data Flow from AWS Config Recorders to the Aggregator
An AWS Config recorder is set up in each account and region, capturing resource configuration states for that account and region. It also records configuration snapshots for that account and region. Also, within that account and region, it applies AWS Config rules to evaluate local resource compliance. AWS Config Aggregator retrieves configuration and compliance data from AWS Config in each source account and region. Once it has collected this data, it aggregates it and presents these results through centralized queries and views.
Querying Aggregated Compliance Data
Aggregating AWS Config datasets from each account and region enables operators to perform advanced queries across the AWS environment. This also gives them visibility into cross-account and cross-region configurations that are unavailable without AWS Config Aggregator. Therefore, security teams can perform centralized compliance analysis, allowing them to more quickly identify configuration drift across environments. They also have a single-query interface that provides organization-wide compliance insights, enabling a holistic approach to configuration compliance management.
Monitoring and Reporting Architecture
Additionally, AWS Config Aggregator enables cross-account monitoring of AWS Config compliance data through an aggregated compliance dashboard for security and governance teams. This enables centralized monitoring of configuration and rule evaluations to detect, report, and remediate configuration drift. Governance teams can perform cross-account compliance reporting from a single governance account. Additionally, this provides seamless integration with audit and regulatory compliance workflows for the AWS environment. This provides security and governance teams with simplified organization-wide compliance monitoring and analysis.
Integrating AWS Config Aggregators with Security Hub
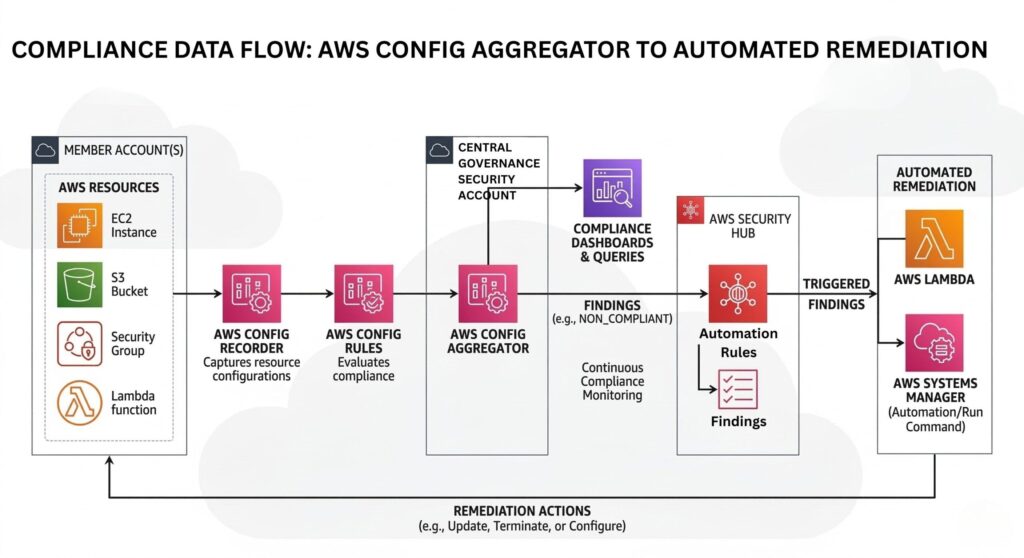
AWS Config as a Compliance Data Source for Security Hub
Compliance findings for monitored resources that are generated by AWS Config rules are still only one part of AWS’s security posture. Therefore, these AWS Config rule evaluations are ingested by Security Hub as security findings. Security Hub is further elaborated in AWS Security Hub Findings: Making Sense of Security Signals. The AWS Config Aggregator feeds continuous compliance monitoring across AWS accounts and regions into Security Hub. This aligns with AWS Foundational Security Best Practices, where config rule results contribute to overall security posture visibility.
Centralized Security Visibility Across AWS Accounts
Feeding aggregated config rule evaluations into Security Hub contributes to organization-wide security findings visibility across AWS accounts. Security teams have access to aggregate compliance insight from either AWS Config or Security Hub. Security teams also have access to unified security posture monitoring for distributed environments by correlating configuration compliance with data from other security sources. Furthermore, they can perform centralized investigations of cross-account security findings.
Governance Automation with Aggregated Compliance Data
An essential aspect of centralized security monitoring is enabling automated remediation workflows that are triggered by compliance findings. Security designers can integrate Lambda functions or System Manager with Security Hub to perform corrective actions. Governance teams can establish automated policy enforcement by having aggregated compliance insights trigger Lambda functions or System Manager. Therefore, these automated governance processes provide continuous compliance validation across AWS accounts and regions.
Best Practices for Enterprise Governance

Use a Dedicated Governance or Security Account
Security best practices recommend hosting the AWS Config Aggregator in a centralized governance account separate from the centralized management account. This follows from establishing trust boundaries where compliance monitoring is separated from production workloads and AWS centralized management. This allows restricting access to configuration governance using least-privilege IAM policies. Therefore, the architecture establishes a clear security and trust boundary for governance operations.
Integrate AWS Aggregator with AWS Organizations
Integrating AWS Config Aggregator with AWS Organizations allows it to perform organization-wide aggregation across member accounts. This also enables it to automatically include newly created accounts within compliance monitoring. Additionally, integration with AWS Organizations simplifies cross-account permissions for configuration and compliance data access. Furthermore, AWS Organizations integration supports maintaining consistent governance policies across all accounts.
Limit Aggregation Scope Where Necessary
The Architecture should restrict aggregation to relevant AWS accounts and regions to prevent noise from obfuscating important signals. Additionally, the AWS Config Aggregator should filter data by governance or compliance requirements to further reduce noise. This will reduce data storage requirements and query overheads when performing analysis. Also, this will improve the performance of the aggregated compliance analysis.
Align Config Rules with Governance Policies
Ultimately, configuration management is enforcing governance policies, so the architecture should map AWS Config Rules to organizational security policies. This includes aligning rule evaluations with regulatory compliance frameworks. Subsequently, centralized monitoring will standardize rule deployment across all AWS accounts. Furthermore, AWS Config Aggregator will support automated enforcement of governance controls.
AWS Config Aggregators: Conclusion
AWS customers inevitably scale up resource use, leading to multi-account architectures to support trust boundaries following security best practices. This leads to configuration compliance visibility and monitoring becoming fragmented across accounts and regions as organizations scale. AWS Config Aggregators address this issue by centralizing configuration monitoring across AWS Accounts and regions. This provides security teams with organization-wide compliance visibility, reducing misinterpretation and making quicker remediation decisions. These aggregated insights also assist governance teams with audit readiness and compliance reporting. Integrating with Security Hub improves security posture through correlations and automated remediation. Meanwhile, integration with AWS Organizations automates the inclusion of all accounts for aggregating their compliance data. In summary, AWS Config Aggregators form a foundational component for enterprise-wide cloud governance.
Further Reading
1. AWS Security, by Dylan Shields
2. AWS Certified Security – Specialty (SCS-C02) Exam Guide, by Adam Book and Stuart Scott
3. AWS Security Cookbook: Practical solutions for securing AWS cloud infrastructure with essential services and best practices by Heartin Kanikathottu
4. Cloud Security Handbook: Effectively secure cloud environments using AWS, Azure, and GCP by Eyal Estrin
Affiliate Disclosure: As an Amazon Associate, I earn from qualifying purchases. This means that if you click on one of the Amazon links and make a purchase, I may receive a small commission at no additional cost to you. This helps support the site and allows me to continue creating valuable content.


